From training
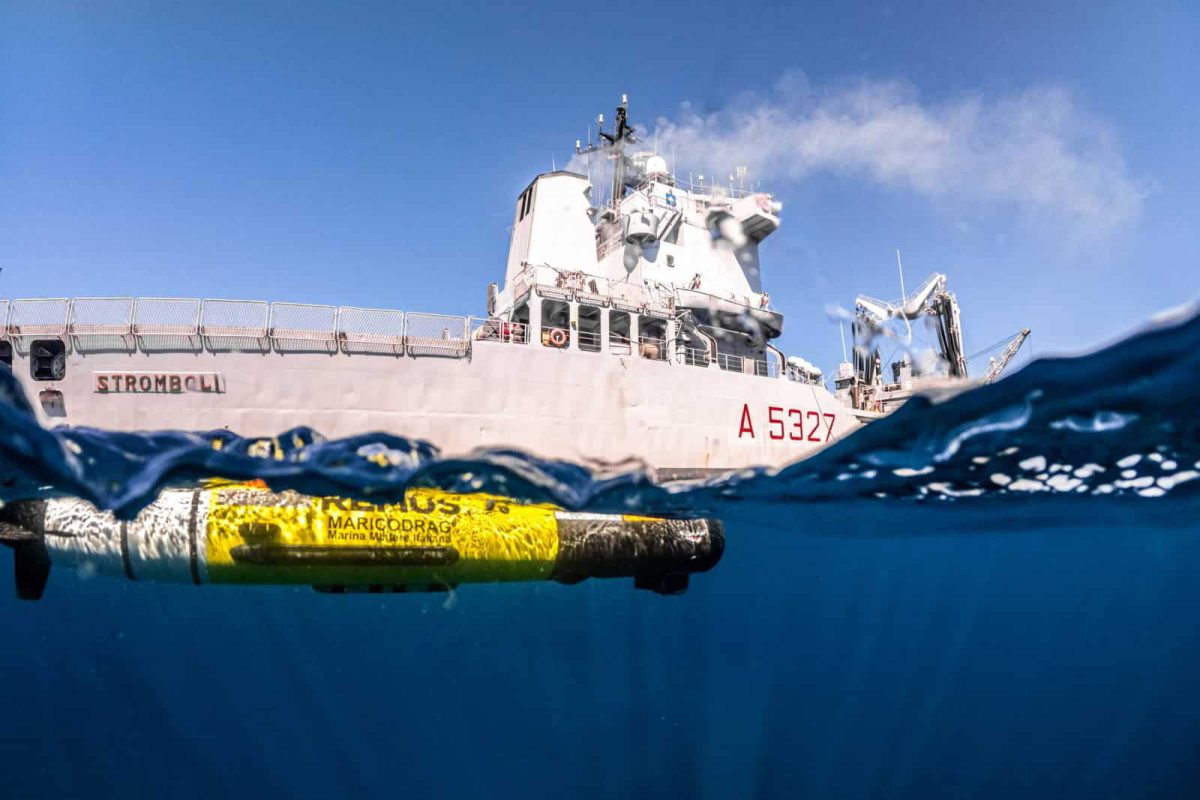
to combat readiness
Plan better, train smarter, reduce workload, improve outcomes, and accelerate readiness with Exonaut
NATO
accredited
25+ years
years of defence innovation
150+
exercises delivered annualy
Global
support of NATO and allied forces
The global standard for training and exercise management
The AI-assisted Exonaut Platform connects headquarters, training centres, regiments, schools and units in one integrated system for planning, design, execution, analysis, and exploitation of training and exercises.
Increases readiness visibility and assurance
Ensures training aligns with strategic direction
Delivers improved, objectives-based outcomes
Enables real-time operations, adaption and evaluation
One Platform for all your training and
exercise management needs
Collective exercises are planned designed and executed across live, virtual and constructive environments.
Readiness status is evaluated against requirements and strategic direction is set.
Exercises are delivered and performance data is captured, evaluated, and assessed against objectives.
Programming & Scheduling
Structure programming. Align activity. Visualise readiness.
Exonaut Programming &. Schdeluling supports headquarters in the strategic programming and synchronization of training events, informed by continuous readiness and risk insight from across the organisation.
Collective Training & Exercise Management
Plan at scale. Control execution. Validate performance.
Exonaut Collective Training & Exercise Management enables structured design, execution, observation, and evaluation of exercises, providing real-time control and objective performance insight to support assured readiness.
In-Unit Training Management
Accelerate planning. Measure outcomes. Assure readiness.
High-Value Candidate Selection
Identify candidates. Capture evidence. Decide with confidence.
Trials & Experimentation Management
Coordinate trials. Validate assessments. Accelerate decisions.
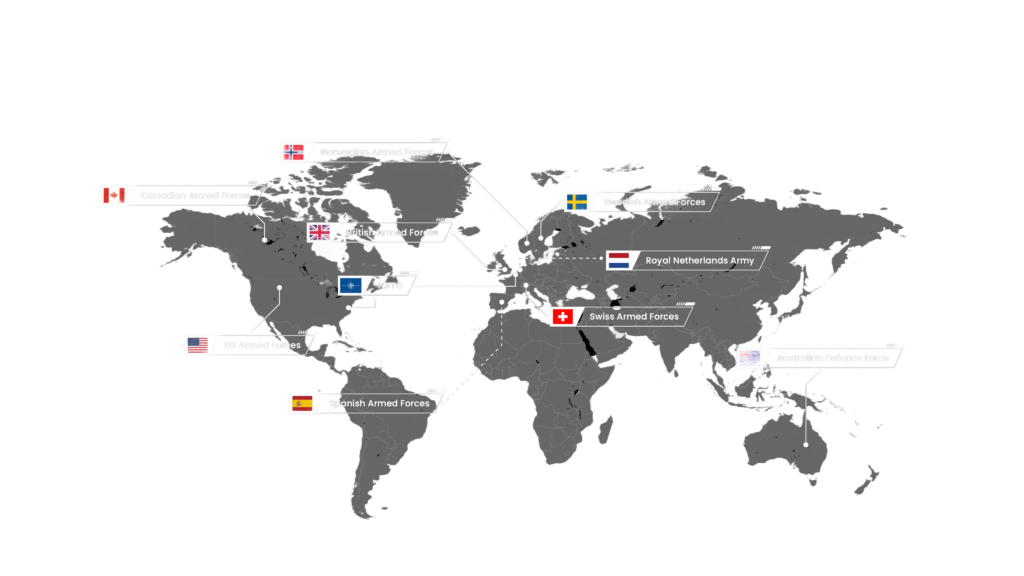
Building Allied Capabilities for over
25 Years
Build a stronger, more resilient organisation with the support of our expert consultants or through our award-winning training and exercise programmes. With over two decades of experience across 100 countries, we help organisations in the military, finance, public, healthcare, utilities, and many other sectors.
Why choose Exonaut?
Military is in our DNA
Many of our staff have served in the
armed forces and remain in the reserves.
This experience is at the core of our abilities to develop and deliver Exonaut, which continues to set the global standard for training and exercise management.
From scoping initial requirements to deployment and testing, to onsite support with the planning, writing and execution of exercises, our defence team are available to support you.
Seamless integration across ecosystem
Many of our staff have served in the
armed forces and remain in the reserves.
This experience is at the core of our abilities to develop and deliver Exonaut, which continues to set the global standard for training and exercise management.
From scoping initial requirements to deployment and testing, to onsite support with the planning, writing and execution of exercises, our defence team are available to support you.
Built for today, designed for the future
Many of our staff have served in the
armed forces and remain in the reserves.
This experience is at the core of our abilities to develop and deliver Exonaut, which continues to set the global standard for training and exercise management.
From scoping initial requirements to deployment and testing, to onsite support with the planning, writing and execution of exercises, our defence team are available to support you.
Innovative, customer-first, COTS software
Many of our staff have served in the
armed forces and remain in the reserves.
This experience is at the core of our abilities to develop and deliver Exonaut, which continues to set the global standard for training and exercise management.
From scoping initial requirements to deployment and testing, to onsite support with the planning, writing and execution of exercises, our defence team are available to support you.